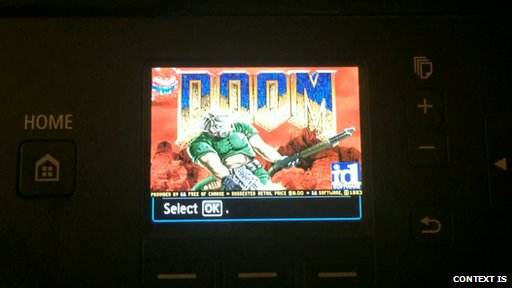
Remember when you needed to shell out a grand or more to get a machine capable of running id Software’s almighty Doom? Now a hacker’s got it running on a printer.
Security researcher Michael Jordon, who works for Context Information Security, set himself the challenge of getting the classic shooter into its unlikely new home as a way of demonstrating the security problems surrounding devices that would form the “internet of things”.
His imagination was sparked when he noticed the printer he was examining, from Canon’s Pixma range, hadn’t been very well secured. Like many other new printers, it comes with Wi-Fi so owners can check the device’s status remotely. However, the web interface does not require a user name or password, meaning anyone can access it once they’ve found it.
Not necessarily disastrous in itself, but Jordon realised you could update the printer’s firmware via this interface. While the firmware was encrypted, Jordon was able to crack it to reveal the core computer code. Reverse-engineering Canon’s encryption system allowed Jordon to write his own firmware that the printer would accept as genuine. This was when it occurred to Jordon to get Doom running on the printer.
“Running Doom, that’s real proof you control the thing,” he told the BBC. “The printer has a 32-bit Arm processor, 10 meg of memory and even the screen is the right size. I had all the bits, but it was a coding problem to get it all running together.”
In the end, it took Jordon four months of work to get Doom on a printer, finishing two days before he was due to give a speech on the project. “The colour palette is still not quite right,” he said. “But it proves the point and it runs quite quickly, though it’s not optimised.”
His point’s been made – Canon has announced that the loophole will be closed as quickly as possible.
Security experts said this could lead to hackers putting backdoors into enterprise networks.
“The larger concern around printer firmware involves the potential to modify it such that the adversary can create backdoors in the device, use the device as a place to launch attacks against the larger network, or specify that all data sent to the printer be stored at the adversary’s preferred location,” said Michael Belton, security assessment lead, Rapid7.
Once the firmware is lost, all bets are off. The fact that this critical functionality is not secure out-of-the-box is a serious flaw in the manufacturer’s design.”